Modern software moves fast—sometimes too fast for security to keep up. As teams chase shorter release cycles and automated rollouts, CI/CD pipelines have quietly become one of the most attractive attack surfaces in today’s DevOps ecosystems. From compromised build servers to poisoned AI models, the common security risks in CI/CD pipelines are no longer theoretical. They are actively exploited, increasingly automated, and often invisible until damage is done.
According to a survey conducted on 500 software testers..
- 53% use continuous integration.
- 38% have continuous delivery.
- 29% rely on continuous deployment.
This guide breaks down the ten most common CI/CD security risks, the role of AI in reshaping both the threats and the defenses, and how SecureSmartz helps organizations stay ahead of modern pipeline attacks. Let’s dive in!
What Is CI/CD Security?
CI/CD security refers to the protection of the Continuous Integration Pipeline and Continuous Deployment Pipeline across every stage—code commits, builds, tests, artifact storage, containerization, and release automation. Unlike traditional application security, CI/CD security focuses on:
- Build systems instead of runtime systems
- Automation scripts instead of application logic
- Configuration Management Tools instead of UI workflows
- Machine identities instead of human users
In cloud-native environments, especially cloud-native CI/CD pipelines, a single misconfiguration can cascade into compromised containers, leaked secrets, or tampered AI models. Here, CI/CD security ensures code integrity across Code Integration & Delivery, secure infrastructure automation, and safe AI-assisted development workflows.
10 Common CI/CD Security Risks (Including AI-Driven Threats)
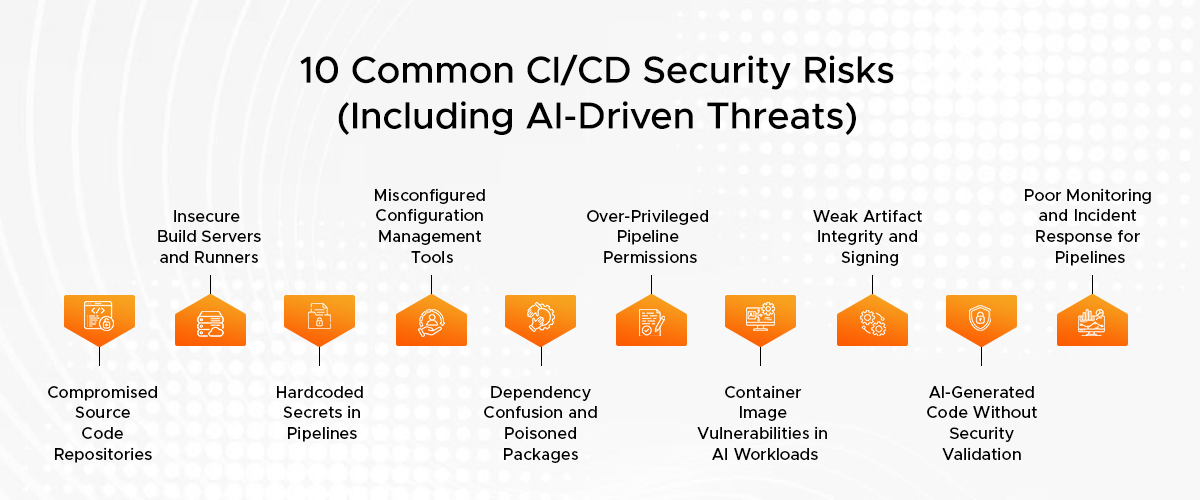
CI/CD pipelines are designed for speed and repeatability—not cybersecurity solutions. As automation deepens and AI-driven tooling becomes common, attackers increasingly target the pipeline itself rather than the application it delivers. Listed below are some of the most critical security risks being faced today:
1. Compromised Source Code Repositories
A CI/CD pipeline is no more reliable than its source code. So, the lack of access controls, leaked tokens, and reused credentials make it easy for hackers to inject malware directly into the code repository.
In AI-assisted development environments, tainted source code files for training can easily find their way into models, especially when source code reviews are rushed. So, why is it dangerous? Because every downstream build inherits the compromise.
2. Insecure Build Servers and Runners
Servers are often operating with superuser privileges and worldwide access. They sit ready to be compromised just by being left unloved and unsecured. This problem is further exacerbated in cloud-native CI/CD pipelines where there can be ephemeral runners that reuse base images that are unsafe.
In other words, cyber attackers can:
- Alter build outputs
- Inject backdoors into artifacts
- Hijack AI model packaging workflows
3. Hardcoded Secrets in Pipelines
API keys, cloud credentials, or signing certificates—all of which can end up either in pipeline scripts or in YAML files. Once they are exposed, these secrets can automatically be harvested by bots crawling through public and private repositories.
In an AI system environment, leaked credentials can also provide exposure to:
- Training datasets
- Model registries
- Inference endpoints
4. Misconfigured Configuration Management Tools
Terraform, Ansible, Helm, CloudFormation, and similar tools are used for automation of the process that makes the infrastructure. So, inconsistencies at this stage are replicated instantly to other environments. This remains one of the most neglected conventional risks to security in the CI/CD pipeline.
A single insecure template can:
- Expose build environments publicly
- Disable logging
- Weaken container isolation
5. Dependency Confusion and Poisoned Packages
Indeed, modern implementations of CI/CD pipelines heavily rely on open-source libraries and AI tools. However, after being ingested, malicious code unleashes itself during builds completely automatically.
As a result, cyber attackers exploit this by:
- Publishing malicious packages with matching internal names
- Injecting tainted ML libraries or pretrained models
- Abusing automated dependency updates
Is your CI/CD pipeline a hidden attack surface?
6. Over-Privileged Pipeline Permissions
CI/CD systems often run with “just make it work” permissions. If attackers have access to the pipeline, they automatically acquire all those privileges. In a nutshell, overprivileged CI/CD pipelines can:
- Modify cloud infrastructure
- Access production data
- Deploy unverified AI services
7. Container Image Vulnerabilities in AI Workloads
Containerized AI development requires huge base images for CUDA libraries, machine learning libraries, as well as system packages. This can lead to a new concern in the context of CI/CD pipelines and containerized AI development, where speed often overrides scrutiny.
Unscanned images may include:
- Known CVEs
- Backdoored binaries
- Unsafe runtime configurations
8. Weak Artifact Integrity and Signing
Trust is broken in silence—and spreads like a wild fire. Without proper verification on artifacts, teams will not be able to determine whether a build has been modified while in transit or in storage.
Unsigned artifacts allow attackers to:
- Replace binaries
- Tamper with AI model files
- Inject malicious containers into registries
9. AI-Generated Code Without Security Validation
The use of artificial intelligence in coding helps CI/CD and configuration management tools speed up coding dramatically, but conversely, these same tools provide yet another set of new threat vectors.
These vectors include:
- Insecure default patterns
- Outdated cryptographic practices
- Hidden logic flaws
10. Poor Monitoring and Incident Response for Pipelines
Many companies track applications, other than pipelines. In the absence of proper incident management software for CI/CD pipelines, the attack remains unnoticed until abnormalities in production environments occur. This is because the occurrence of pipeline leaks is not accompanied by the sending of traditional alerts.
CI/CD Pipeline Security Best Practices (AI-Enhanced)
Securing CI/CD pipelines requires more than static rules or periodic audits. Modern pipelines demand adaptive, intelligence-driven defenses that evolve alongside automation and AI tooling. Here are some proven strategies to ensure CI/CD pipeline security:
-
Shift Security Left—And Automate It
Security must begin at commit time, not deployment time. You should focus on early CI/CD workflow improvement without slowing developers. Here, AI-assisted scanners can help analyze pull requests, infrastructure templates, and AI training scripts.
-
Apply Least Privilege Everywhere
AI tools can continuously analyze permission drift and flag risky expansions. You can use these tools to reduce blast radius by enforcing scoped tokens, role-based access, and short-lived credentials.
-
Secure Container and AI Artifacts
Following a set of measures is essential for DevSecOps pipeline optimization in AI-heavy environments. This means you need to adopt image signing, model checksum verification, and policy-based admission controls.
-
Monitor Pipelines Like Production Systems
Use behavior-based detection instead of static rules. Here, AI-driven monitoring can help you spot unusual build patterns, suspicious dependency changes, and unexpected deployment paths.
How SecureSmartz Addresses CI/CD Pipeline Security?
For more than 26 years, SecureSmartz has been tackling the security aspects of CI/CD pipes via continuous risk management techniques made possible by intelligent automation and human intelligence. Here’s how we can help you ensure secure CI/CD pipelines in the AI-powered digital world:
- AI-Enhanced Pipeline Threat Modeling: We employ artificial intelligence-driven analysis to determine pipeline attack paths by indicating areas where automation, credentials, and artificial intelligence paths intersect.
- Continuous Security Validation: Our solutions also comply with the Code Integration and Delivery processes for risk analysis in real-time without impacting velocity.
- Smart Configuration Audits: We assess Configuration Management Tools using AI-driven drift detection to uncover silent misconfigurations before they scale.
- Advanced Incident Readiness: SecureSmartz implements tailored incident management tools for CI/CD pipelines that reduce the time for incident identification, diagnosis, and isolation.
- Secure AI & Container Pipelines: We specialize in the best solutions for CI/CD pipelines in containerized AI development, starting from model integrity to image security.
The Bottom Line
CI/CD pipelines are no longer just delivery mechanisms—they are high-value targets. As AI accelerates development and automation deepens, the common security risks in CI/CD pipelines grow more complex, more automated, and more damaging. Organizations that secure pipelines proactively—using intelligence, automation, and continuous oversight—don’t just reduce risk. They ship faster, safer, and with confidence. So, are you ready to build pipelines that deserve trust?
Frequently Asked Questions
- Insecure repositories
- Leaked secrets
- Misconfigured automation tools
- Vulnerable containers
- Poisoned dependencies
- Weak pipeline monitoring